Validation of the National Institutes of Health Stroke Scale-8 to Detect Large Vessel Occlusion in Ischemic Stroke - Journal of Stroke and Cerebrovascular Diseases

Riverdude Covers on Twitter: "I swear to God, people think Heaven Door can do literally anything Heal a broken bone, make you fly, warp space time, you name it, people have thought
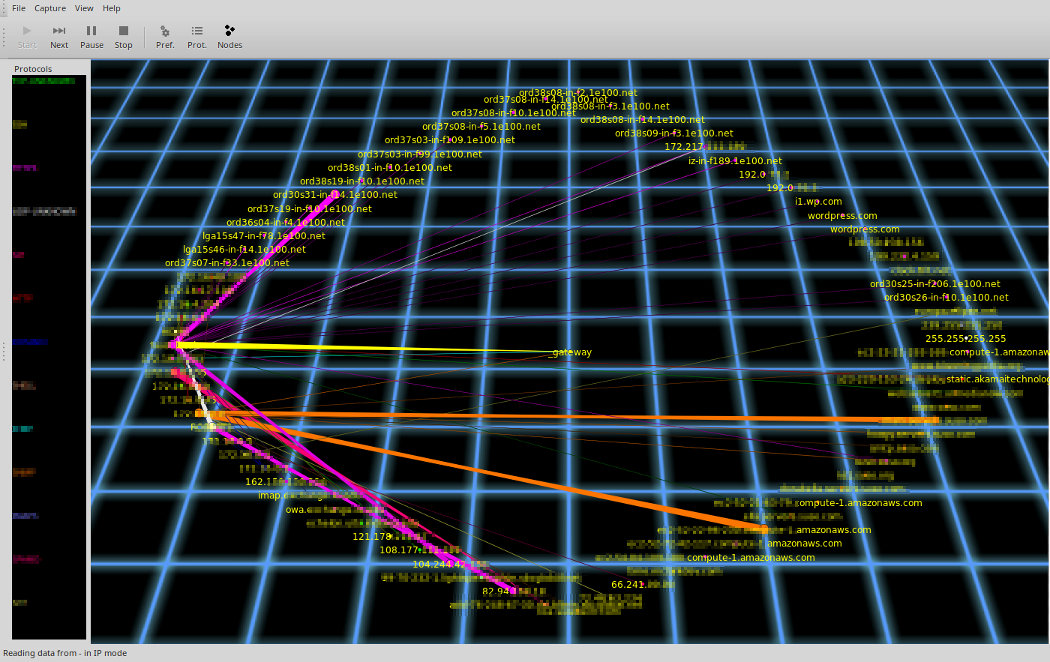
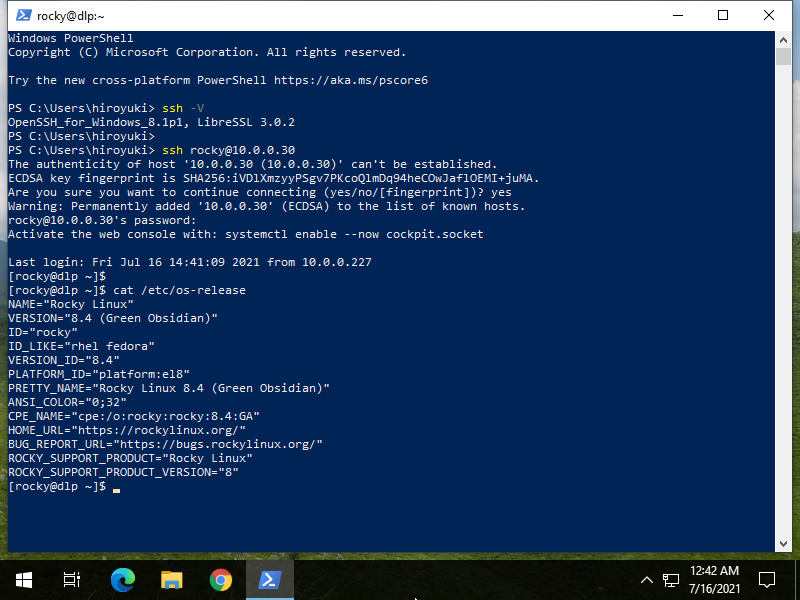
Command Line Magic on Twitter: "ssh root@192.168.0.1 tcpdump -n -i any -w- 'not \( port 22 and host 192.168.0.1 \)' |etherape -r- # Instant visualization of linux router traffic. Yes, root on

GitHub - RamonLucio/Born2beRoot: This project aims to introduce you to the wonderful world of virtualization.
Stanley Milgram Quote: “Some system of authority is a requirement of all communal living, and it is only the man dwelling in isolation who is no...”



![NIH STROKE SCALE Interval: 1[ ] Baseline 2[ ] 2 hours ... - Medscape NIH STROKE SCALE Interval: 1[ ] Baseline 2[ ] 2 hours ... - Medscape](https://img.yumpu.com/43645244/1/500x640/nih-stroke-scale-interval-1-baseline-2-2-hours-medscape.jpg)